-
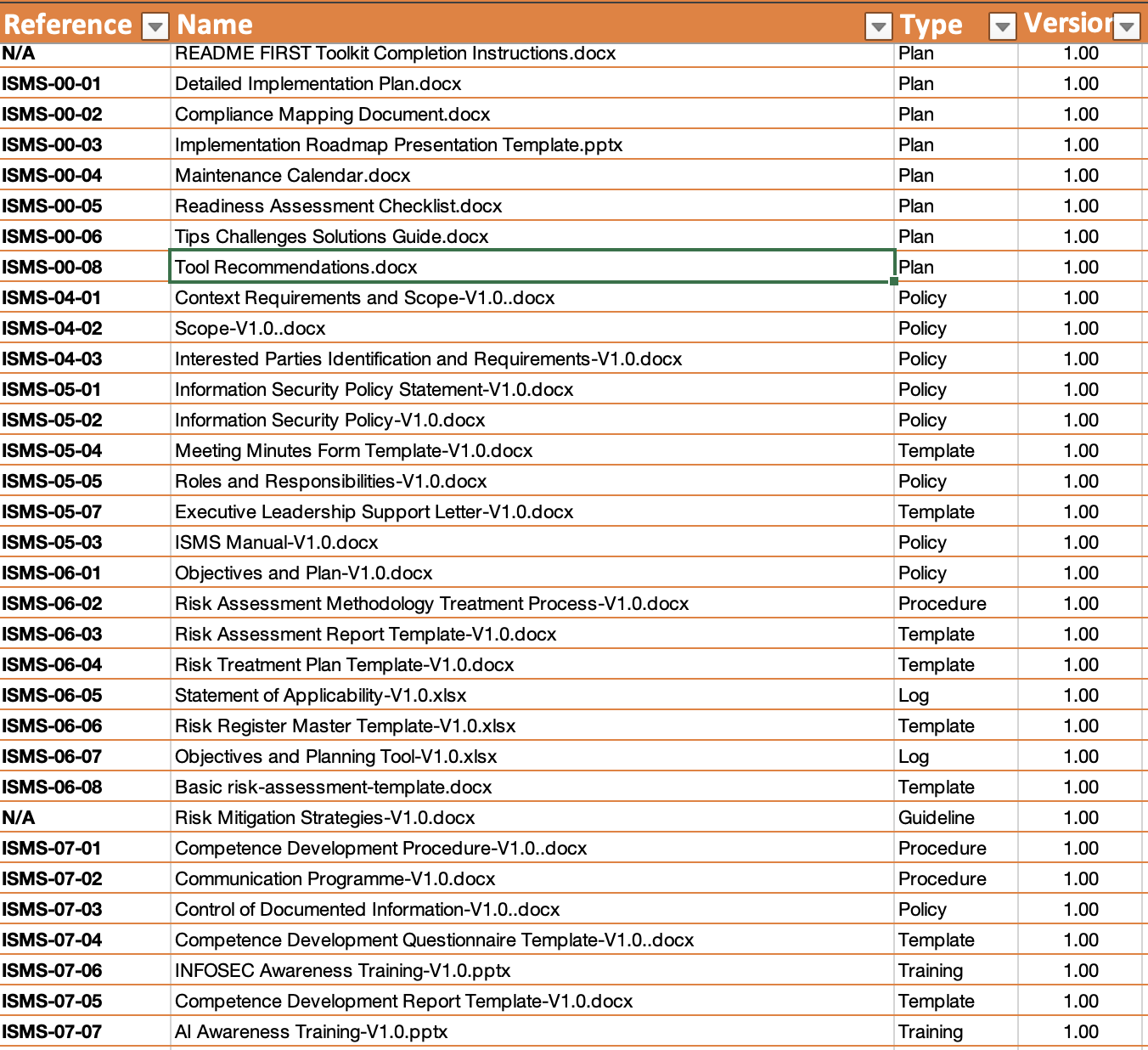
README FIRST Toolkit Completion Instructions.docx
Detailed Implementation Plan.docx
Compliance Mapping Document.docx
Implementation Roadmap Presentation Template.pptx
Maintenance Calendar.docx
Readiness Assessment Checklist.docx
Tips Challenges Solutions Guide.docx
Tool Recommendations.docx
-
Context Requirements and Scope-V1.0..docx
Scope-V1.0..docx
Interested Parties Identification and Requirements-V1.0.docx
-
Information Security Policy Statement-V1.0.docx
Information Security Policy-V1.0.docx
Meeting Minutes Form Template-V1.0.docx
Roles and Responsibilities-V1.0.docx
Executive Leadership Support Letter-V1.0.docx
ISMS Manual-V1.0.docx
-
Objectives and Plan-V1.0.docx
Risk Assessment Methodology Treatment Process-V1.0.docx
Risk Assessment Report Template-V1.0.docx
Risk Treatment Plan Template-V1.0.docxStatement of Applicability-V1.0.xlsx
Risk Register Master Template-V1.0.xlsx
Objectives and Planning Tool-V1.0.xlsx
Basic risk-assessment-template.docx
Risk Mitigation Strategies-V1.0.docx
-
Competence Development Procedure-V1.0..docx
Communication Programme-V1.0.docx
Control of Documented Information-V1.0..docx
Competence Development Questionnaire Template-V1.0..docx
INFOSEC Awareness Training-V1.0.pptx
Competence Development Report Template-V1.0.docx
AI Awareness Training-V1.0.pptx
Phishing Cyber Threats Training-V1.0.pptx
Secure Code Development Awareness-V1.0.pptx
Documentation Log-V1.0.xlsx
-
SOP template.doc
Operational Planning and Control Procedure-V1.0.docx
-
Monitoring, Measurement, Analysis, and Evaluation Process.docx
Internal Audit Procedure.docx
Internal Audit Plan Template-V1.0.docx
Internal Audit Nonconformance Action Plan Template-V1.0.docx
Internal Audit Report Template-V1.0..docx
Internal Audit Checklist Template-V1.0.docx
Internal Audit Schedule.xlsx
Procedure for Management Reviews-V1.0.docx
Management Review Meeting Agenda Template-V1.0.docx
-
5-Whys-Template.docx
Fishbone-Diagram-Template.docx
Management of Nonconformities Procedure.docx
Corrective Action Plan Form Template.docx
Regular Activity Schedule.xlsx
Nonconformity and Corrective Action Log.xlsx
-
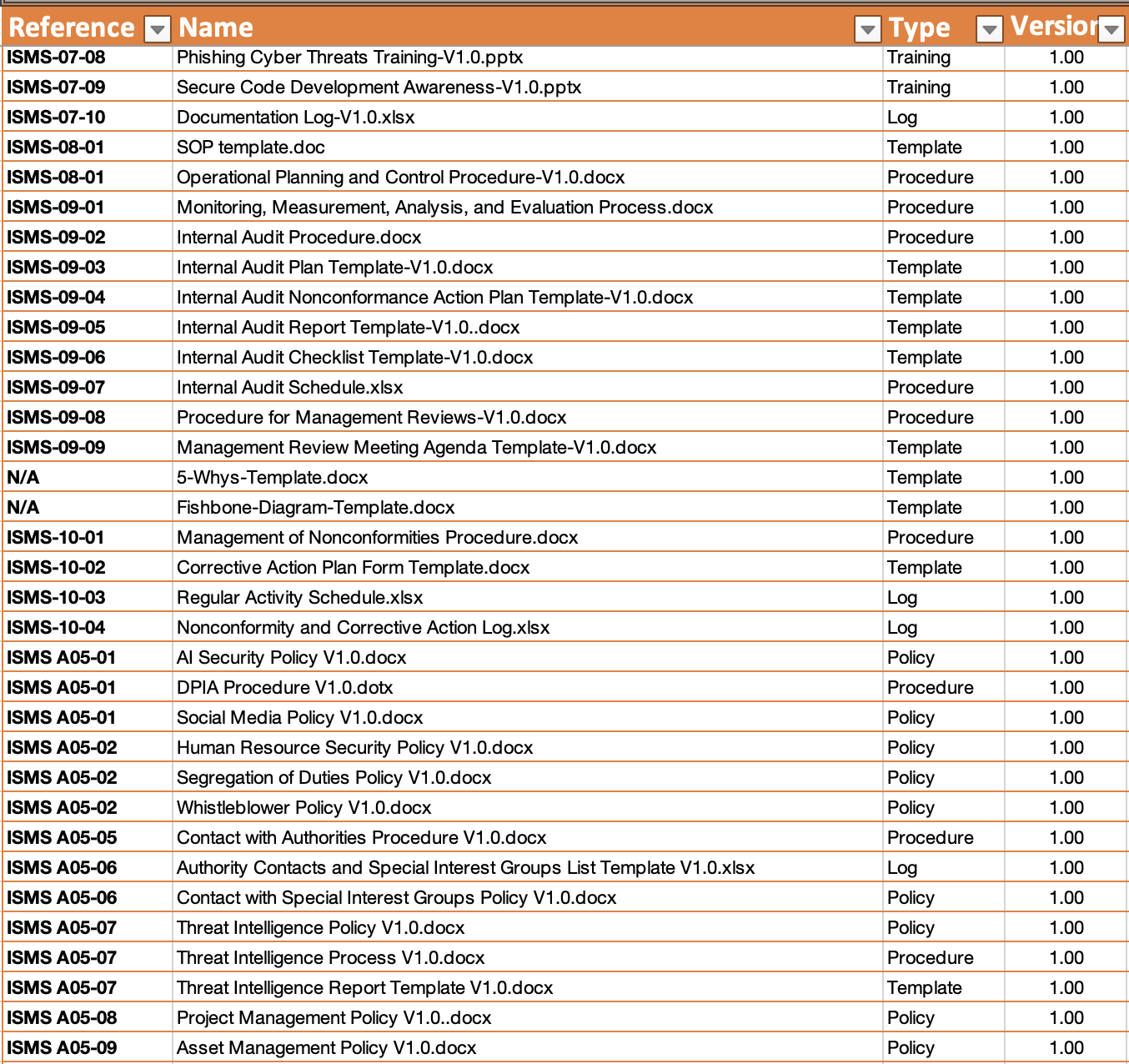
AI Security Policy V1.0.docx
DPIA Procedure V1.0.dotx
Social Media Policy V1.0.docx
Human Resource Security Policy V1.0.docx
Segregation of Duties Policy V1.0.docx
Whistleblower Policy V1.0.docx
Contact with Authorities Procedure V1.0.docx
Authority Contacts and Special Interest Groups List Template V1.0.xlsx
Contact with Special Interest Groups Policy V1.0.docx
Threat Intelligence Policy V1.0.docx
Threat Intelligence Process V1.0.docx
Threat Intelligence Report Template V1.0.docx
Project Management Policy V1.0..docx
Asset Management Policy V1.0.docx
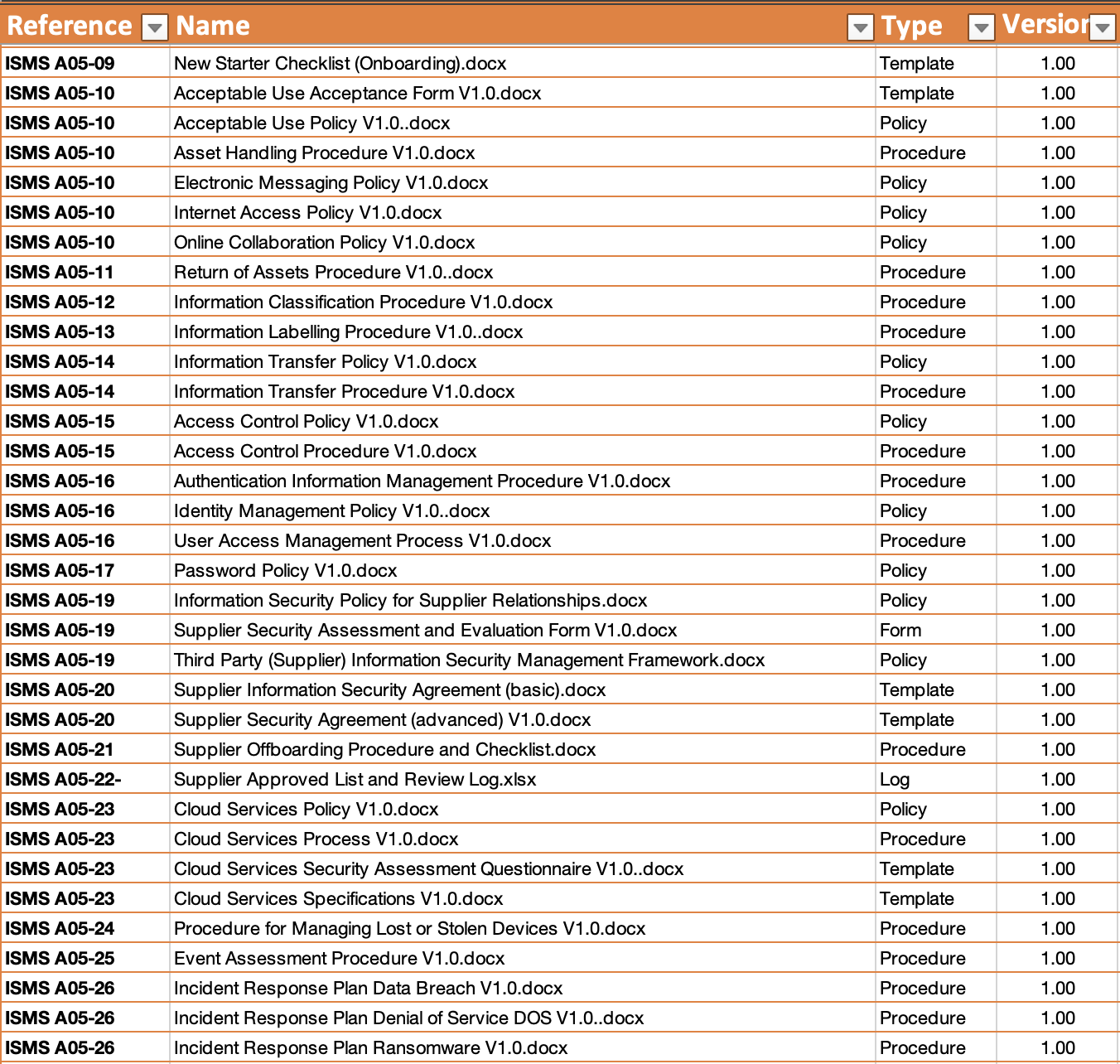
New Starter Checklist (Onboarding).docx
Acceptable Use Acceptance Form V1.0.docx
Acceptable Use Policy V1.0..docx
Asset Handling Procedure V1.0.docx
Electronic Messaging Policy V1.0.docx
Internet Access Policy V1.0.docx
Online Collaboration Policy V1.0.docx
Return of Assets Procedure V1.0..docx
Information Classification Procedure V1.0.docx
Information Labelling Procedure V1.0..docx
Information Transfer Policy V1.0.docx
Information Transfer Procedure V1.0.docx
Access Control Policy V1.0.docx
Access Control Procedure V1.0.docx
Authentication Information Management Procedure V1.0.docx
Identity Management Policy V1.0..docx
User Access Management Process V1.0.docx
Password Policy V1.0.docx
Information Security Policy for Supplier Relationships.docx
Supplier Security Assessment and Evaluation Form V1.0.docx
Third Party (Supplier) Information Security Management Framework.docx
Supplier Information Security Agreement (basic).docx
Supplier Security Agreement (advanced) V1.0.docx
Supplier Offboarding Procedure and Checklist.docx
Supplier Approved List and Review Log.xlsx
Cloud Services Policy V1.0.docxCloud Services Process V1.0.docx
Cloud Services Security Assessment Questionnaire V1.0..docx
Cloud Services Specifications V1.0.docx
Procedure for Managing Lost or Stolen Devices V1.0.docx
Event Assessment Procedure V1.0.docx
Incident Response Plan Data Breach V1.0.docx
Incident Response Plan Denial of Service DOS V1.0..docx
Incident Response Plan Ransomware V1.0.docx
Incident Response Procedure V1.0.docx
Incident Lessons Learned Report V1.0.docx
Evidence Collection Procedure V1.0..docx
Business Impact Analysis Process V1.0.docx
Business Impact Analysis Report V1.0.docx
ICT Continuity Incident Response Procedure V1.0.docx
ICT Continuity Plan V1.0.docx
ICT Continuity Test Plan V1.0.docx
ICT Continuity Test Report V1.0.docx
Legal Regulatory and Contractual Requirements Procedure V1.0..docx
IP and Copyright Policy V1.0.docx
Records Retention and Protection Policy V1.0.docx
Personal Data Breach Notification Form V1.0.docx
Personal Data Breach Notification Letter V1.0.docx
Personal Data Breach Notification Procedure V1.0.docx
Privacy and Personal Data Protection Policy V1.0.docx
-
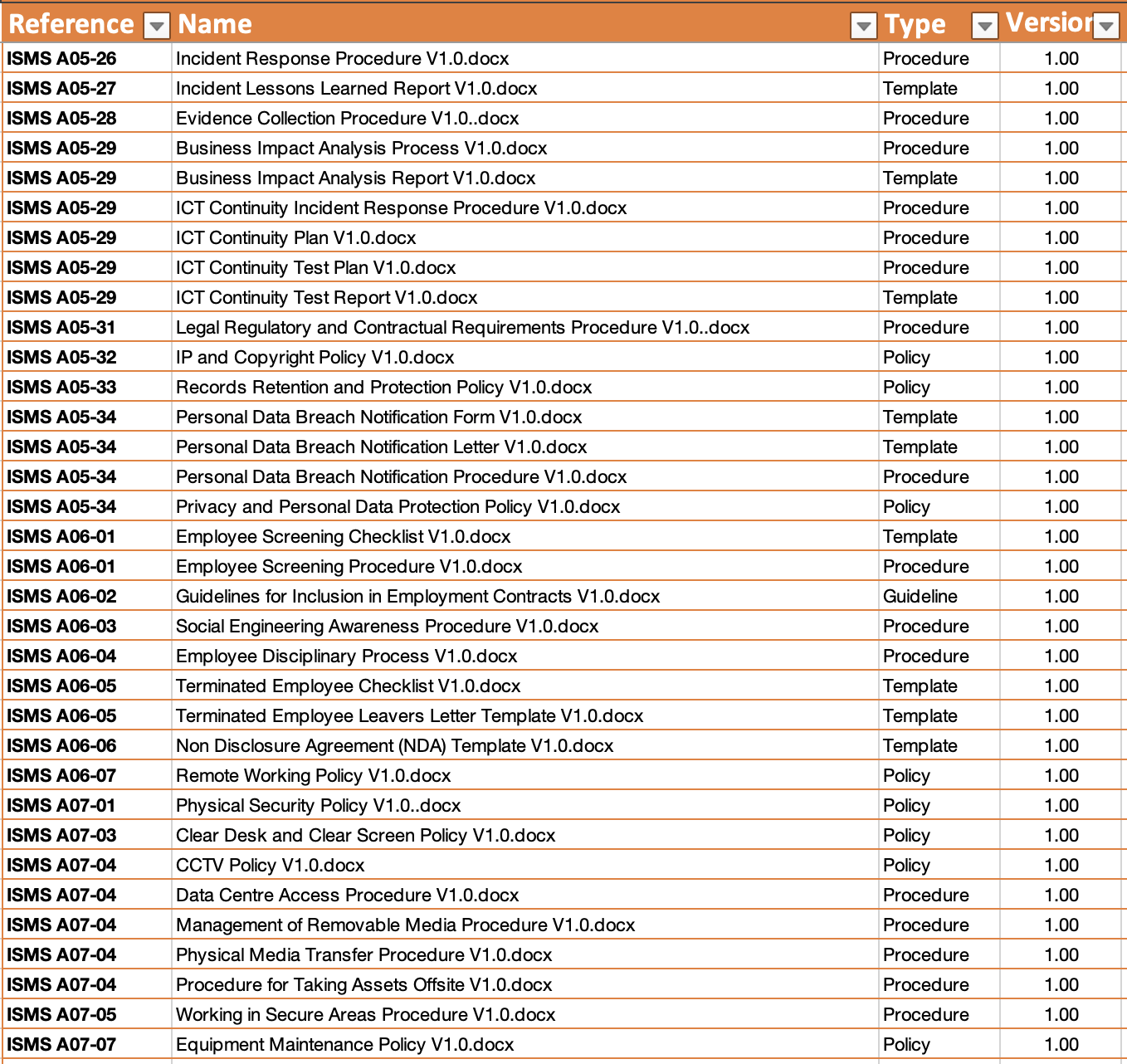
Employee Screening Checklist V1.0.docx
Employee Screening Procedure V1.0.docx
Guidelines for Inclusion in Employment Contracts V1.0.docx
Social Engineering Awareness Procedure V1.0.docx
Employee Disciplinary Process V1.0.docx
Terminated Employee Checklist V1.0.docx
Terminated Employee Leavers Letter Template V1.0.docx
Non Disclosure Agreement (NDA) Template V1.0.docx
Remote Working Policy V1.0.docx
-
Physical Security Policy V1.0..docx
Clear Desk and Clear Screen Policy V1.0.docx
CCTV Policy V1.0.docx
Data Centre Access Procedure V1.0.docx
Management of Removable Media Procedure V1.0.docx
Physical Media Transfer Procedure V1.0.docx
Procedure for Taking Assets Offsite V1.0.docx
Working in Secure Areas Procedure V1.0.docx
Equipment Maintenance Policy V1.0.docx
Disposal of Media Procedure V1.0.docx
Supporting Utilities Policy V1.0.docx
Cabling Security Policy V1.0.docx
Physical Security Design Standards V1.0.docx
-
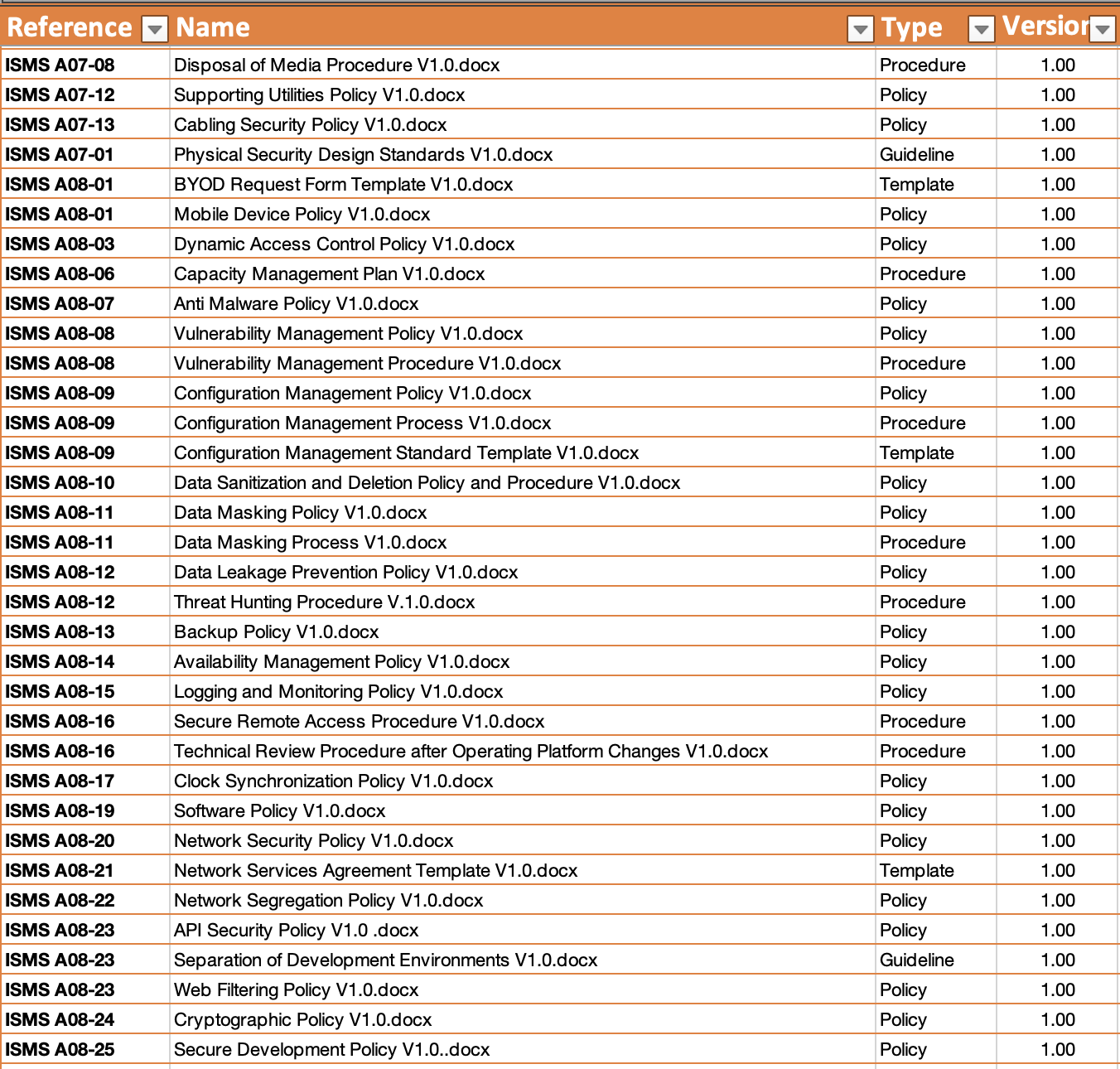
BYOD Policy V1.0.docx
BYOD Request Form Template V1.0.docx
Mobile Device Policy V1.0.docx
Dynamic Access Control Policy V1.0.docx
Capacity Management Plan V1.0.docx
Anti Malware Policy V1.0.docx
Vulnerability Management Policy V1.0.docx
Vulnerability Management Procedure V1.0.docx
Configuration Management Policy V1.0.docx
Configuration Management Process V1.0.docx
Configuration Management Standard Template V1.0.docx
Data Sanitization and Deletion Policy and Procedure V1.0.docx
Data Masking Policy V1.0.docx
Data Masking Process V1.0.docx
Data Leakage Prevention Policy V1.0.docx
Threat Hunting Procedure V.1.0.docx
Backup Policy V1.0.docx
Availability Management Policy V1.0.docx
Logging and Monitoring Policy V1.0.docx
Secure Remote Access Procedure V1.0.docx
Technical Review Procedure after Operating Platform Changes V1.0.docx
Clock Synchronization Policy V1.0.docx
Software Policy V1.0.docx
Network Security Policy V1.0.docx
Network Services Agreement Template V1.0.docx
Network Segregation Policy V1.0.docx
API Security Policy V1.0 .docxSeparation of Development Environments V1.0.docx
Web Filtering Policy V1.0.docx
Cryptographic Policy V1.0.docx
Secure Development Policy V1.0..docx
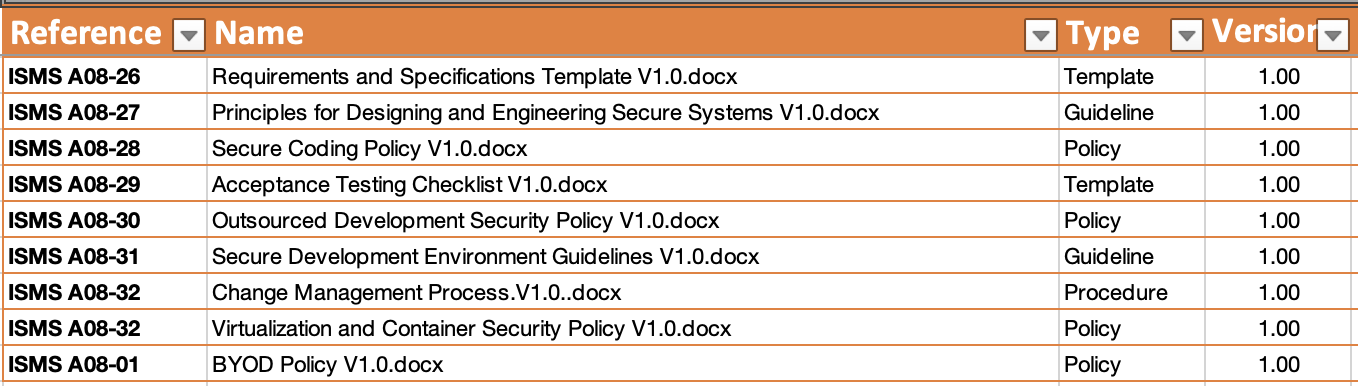
Requirements and Specifications Template V1.0.docx
Principles for Designing and Engineering Secure Systems V1.0.docx
Secure Coding Policy V1.0.docxAcceptance Testing Checklist V1.0.docx
Outsourced Development Security Policy V1.0.docx
Secure Development Environment Guidelines V1.0.docx
Change Management Process.V1.0..docx
Virtualization and Container Security Policy V1.0.docx